 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 How to configure highly available remote logins (such as SSH and Telnet) on Linux
How to configure highly available remote logins (such as SSH and Telnet) on Linux
How to configure highly available remote logins (such as SSH and Telnet) on Linux
Jul 05, 2023 am 11:10 AMHow to configure high-availability remote login (such as SSH and Telnet) on Linux
Abstract: Remote login is one of the most commonly used functions in Linux systems, which allows us to connect to remote hosts through the network and operate. In practical applications, in order to ensure system availability and security, the remote login service needs to be configured in high availability mode. This article will introduce how to configure highly available remote login on Linux, including SSH and Telnet, and provide relevant code examples.
1. SSH configuration
SSH (Secure Shell) is a remote login protocol based on encryption technology. Secure remote login can be achieved through SSH in an unsecured network. The following are the steps to configure SSH high availability:
- Install and configure SSH server
In Linux systems, the commonly used software package for SSH servers is OpenSSH. First, we need to ensure that the OpenSSH package is installed on the host machine.
$ sudo apt-get install openssh-server # Ubuntu/Debian
$ sudo yum install openssh-server # CentOS/RHEL
After the installation is completed, the SSH server will automatically Starts and listens on the default port 22.
- Configure SSH communication key
In order to achieve high availability, we can use an SSH communication key pair for authentication instead of using the traditional username/password.
First, we need to generate an SSH key pair:
$ ssh-keygen -t rsa
Then, copy the public key to all remote hosts:
$ ssh-copy-id remote_host
- Configuring SSH load balancing
In order to achieve high availability of SSH, we can use load balancing to distribute remote login requests to multiple on a host. Commonly used load balancing software include HAProxy and Nginx.
Taking HAProxy as an example, first install HAProxy:
$ sudo apt-get install haproxy # Ubuntu/Debian
$ sudo yum install haproxy # CentOS/RHEL
Then, edit the HAProxy configuration file:
$ sudo vi /etc/haproxy/haproxy.cfg
Add the following configuration block in the file:
frontend ssh
bind *:22 mode tcp default_backend ssh_servers
backend ssh_servers
mode tcp balance roundrobin server ssh1 192.168.1.101:22 check server ssh2 192.168.1.102:22 check server ssh3 192.168.1.103:22 check
Save and exit the file, then restart the HAProxy service:
$ sudo systemctl restart haproxy
Now you can use HAProxy to provide IP address to connect to the SSH server.
2. Telnet configuration
Telnet is a protocol used for remote login, but it does not have the encryption function like SSH, so it is not suitable for use in insecure networks. The following are the steps to configure Telnet high availability:
- Install and configure Telnet server
In Linux systems, the commonly used software package for Telnet servers is telnetd. First, we need to ensure that the telnetd package has been installed on the host (example: CentOS/RHEL):
$ sudo yum install telnet-server
After the installation is complete, the Telnet server will Starts automatically and listens on the default port 23.
- Configuring Telnet Load Balancing
Similar to SSH, we can use load balancing to achieve high availability of Telnet. In Linux, we can use iptables and netfilter to achieve load balancing.
First, edit the iptables configuration file:
$ sudo vi /etc/sysctl.conf
Add the following configuration at the end of the file:
net.ipv4.ip_forward = 1
Save and exit the file, then load the configuration file:
$ sudo sysctl -p
Next, execute the following command to configure load balancing :
$ sudo iptables -t nat -A PREROUTING -p tcp --dport 23 -j DNAT --to-destination
$ sudo iptables -t nat -A POSTROUTING - j MASQUERADE
Where,
- Configuring Service Discovery
In order to achieve high availability, we need to find a way to distribute client requests to multiple Telnet servers. Commonly used service discovery software include ZooKeeper and Consul.
Taking ZooKeeper as an example, first install ZooKeeper:
$ sudo apt-get install zookeeperd # Ubuntu/Debian
$ sudo yum install zookeeper # CentOS/RHEL
Then, edit the ZooKeeper configuration file:
$ sudo vi /etc/zookeeper/conf/zoo.cfg
Add the following configuration to the file:
server. 1=zoo1:2888:3888
server.2=zoo2:2888:3888
server.3=zoo3:2888:3888
where zoo1, zoo2, and zoo3 are the host names of the ZooKeeper server .
Save and exit the file, then restart the ZooKeeper service:
$ sudo service zookeeper restart
Now you can connect to the Telnet server using the IP address provided by ZooKeeper.
Conclusion
By configuring a highly available remote login service, we can ensure the availability and security of the system. This article describes how to configure high availability of SSH and Telnet on Linux and provides relevant code examples. I hope this article can be helpful to you, thank you for reading!
The above is the detailed content of How to configure highly available remote logins (such as SSH and Telnet) on Linux. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undress AI Tool
Undress images for free

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)
 How does the cost of ownership differ between Linux and Windows?
Jun 09, 2025 am 12:17 AM
How does the cost of ownership differ between Linux and Windows?
Jun 09, 2025 am 12:17 AM
Linux's cost of ownership is usually lower than Windows. 1) Linux does not require license fees, saving a lot of costs, while Windows requires purchasing a license. 2) Linux has low hardware requirements and can extend the service life of the device. 3) The Linux community provides free support to reduce maintenance costs. 4) Linux is highly secure and reduces productivity losses. 5) The Linux learning curve is steep, but Windows is easier to use. The choice should be based on specific needs and budget.
 How to install Linux alongside Windows (dual boot)?
Jun 18, 2025 am 12:19 AM
How to install Linux alongside Windows (dual boot)?
Jun 18, 2025 am 12:19 AM
The key to installing dual systems in Linux and Windows is partitioning and boot settings. 1. Preparation includes backing up data and compressing existing partitions to make space; 2. Use Ventoy or Rufus to make Linux boot USB disk, recommend Ubuntu; 3. Select "Coexist with other systems" or manually partition during installation (/at least 20GB, /home remaining space, swap optional); 4. Check the installation of third-party drivers to avoid hardware problems; 5. If you do not enter the Grub boot menu after installation, you can use boot-repair to repair the boot or adjust the BIOS startup sequence. As long as the steps are clear and the operation is done properly, the whole process is not complicated.
 How to enable the EPEL (Extra Packages for Enterprise Linux) repository?
Jun 17, 2025 am 09:15 AM
How to enable the EPEL (Extra Packages for Enterprise Linux) repository?
Jun 17, 2025 am 09:15 AM
The key to enabling EPEL repository is to select the correct installation method according to the system version. First, confirm the system type and version, and use the command cat/etc/os-release to obtain information; second, enable EPEL through dnfinstallepel-release on CentOS/RockyLinux, and the 8 and 9 version commands are the same; third, you need to manually download the corresponding version of the .repo file and install it on RHEL; fourth, you can re-import the GPG key when encountering problems. Note that the old version may not be supported, and you can also consider enabling epel-next to obtain the test package. After completing the above steps, use dnfrepolist to verify that the EPEL repository is successfully added.
 How to choose a Linux distro for a beginner?
Jun 19, 2025 am 12:09 AM
How to choose a Linux distro for a beginner?
Jun 19, 2025 am 12:09 AM
Newbie users should first clarify their usage requirements when choosing a Linux distribution. 1. Choose Ubuntu or LinuxMint for daily use; programming and development are suitable for Manjaro or Fedora; use Lubuntu and other lightweight systems for old devices; recommend CentOSStream or Debian to learn the underlying principles. 2. Stability is preferred for UbuntuLTS or Debian; you can choose Arch or Manjaro to pursue new features. 3. In terms of community support, Ubuntu and LinuxMint are rich in resources, and Arch documents are technically oriented. 4. In terms of installation difficulty, Ubuntu and LinuxMint are relatively simple, and Arch is suitable for those with basic needs. It is recommended to try it first and then decide.
 How to add a new disk to Linux
Jun 27, 2025 am 12:15 AM
How to add a new disk to Linux
Jun 27, 2025 am 12:15 AM
The steps to add a new hard disk to the Linux system are as follows: 1. Confirm that the hard disk is recognized and use lsblk or fdisk-l to check; 2. Use fdisk or parted partitions, such as fdisk/dev/sdb and create and save; 3. Format the partition to a file system, such as mkfs.ext4/dev/sdb1; 4. Use the mount command for temporary mounts, such as mount/dev/sdb1/mnt/data; 5. Modify /etc/fstab to achieve automatic mount on the computer, and test the mount first to ensure correctness. Be sure to confirm data security before operation to avoid hardware connection problems.
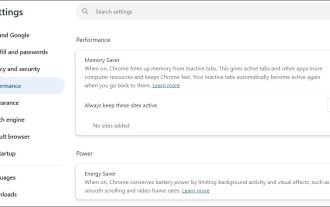 Fixed the failure to upload files in Windows Google Chrome
Jul 08, 2025 pm 02:33 PM
Fixed the failure to upload files in Windows Google Chrome
Jul 08, 2025 pm 02:33 PM
Have problems uploading files in Google Chrome? This may be annoying, right? Whether you are attaching documents to emails, sharing images on social media, or submitting important files for work or school, a smooth file upload process is crucial. So, it can be frustrating if your file uploads continue to fail in Chrome on Windows PC. If you're not ready to give up your favorite browser, here are some tips for fixes that can't upload files on Windows Google Chrome 1. Start with Universal Repair Before we learn about any advanced troubleshooting tips, it's best to try some of the basic solutions mentioned below. Troubleshooting Internet connection issues: Internet connection
 Where are system logs located in Linux?
Jun 24, 2025 am 12:15 AM
Where are system logs located in Linux?
Jun 24, 2025 am 12:15 AM
Logs in Linux systems are usually stored in the /var/log directory, which contains a variety of key log files, such as syslog or messages (record system logs), auth.log (record authentication events), kern.log (record kernel messages), dpkg.log or yum.log (record package operations), boot.log (record startup information); log content can be viewed through cat, tail-f or journalctl commands; application logs are often located in subdirectories under /var/log, such as Apache's apache2 or httpd directory, MySQL log files, etc.; at the same time, it is necessary to note that log permissions usually require s
 What is the sudo command and when should I use it?
Jul 02, 2025 am 12:20 AM
What is the sudo command and when should I use it?
Jul 02, 2025 am 12:20 AM
sudo stands for "substituteuserdo" or "superuserdo", allowing users to run commands with permissions of other users (usually root). Its core uses include: 1. Perform system-level operations such as installing software or editing system files; 2. Accessing protected directories or logs; 3. Manage services such as restarting nginx; 4. Modify global settings such as /etc/hosts. When using it, the system will check the /etc/sudoers configuration and verify the user password, provide temporary permissions instead of continuously logging in as root, ensuring security. Best practices include: only when necessary, avoid blindly executing network commands, editing sudoers files with visudo, and considering continuous operations.





