Linux user and group management ensures proper access control and system organization through user accounts and group memberships. 2. Users have unique UIDs and are categorized as regular users or the root user (UID 0), while groups simplify permission assignments by grouping users. 3. Key commands include sudo adduser to create users, sudo passwd to set passwords, sudo deluser or sudo userdel to delete users, and sudo usermod to modify user properties like primary group, supplementary groups, shell, or account lock status. 4. Groups are managed using sudo groupadd to create, sudo groupdel to delete, sudo usermod -aG to add users to groups, and sudo gpasswd -d to remove users from groups, with groups username or id username used to view memberships. 5. Core configuration files include /etc/passwd for user info, /etc/shadow for encrypted passwords, /etc/group for group definitions, and /etc/gshadow for group passwords, all of which should not be edited manually to prevent errors. 6. Best practices include avoiding root for daily tasks, using groups for access control like docker, auditing accounts regularly, enforcing strong passwords, disabling unused accounts, and setting appropriate default permissions. 7. In a practical example, creating a developers group, adding users to it, and setting up a shared directory with proper group ownership and 775 permissions allows collaborative access securely. Mastering these tools and practices enables efficient, secure, and organized Linux system administration.

Managing users and groups is a fundamental part of Linux system administration. Whether you're setting up a personal machine or managing a server, understanding how to create, modify, and secure user accounts and groups ensures proper access control and system organization. Here’s a practical guide to help you master Linux user and group management.

1. Understanding Users and Groups in Linux
In Linux, every process runs under a user account, and each file or directory is owned by a user and a group. This ownership determines who can read, write, or execute resources.
-
Users: Each user has a unique username and user ID (UID). There are two main types:
- Regular users: For everyday tasks.
- Root user: The superuser with full system privileges (UID 0).
- Groups: A collection of users. Each user belongs to at least one group (primary group), and can be added to multiple supplementary groups. Groups simplify permission management.
Files and directories use permission bits (read, write, execute) for the owner, group, and others.

2. Managing User Accounts
You can manage users using command-line tools. Most of these require sudo or root access.
Common User Commands
-
Create a user:

sudo adduser username
This command is user-friendly and prompts you to set a password and fill in user details.
Alternatively, use the lower-level:
sudo useradd username
You may need to manually set a password with
sudo passwd username. Set or change a password:
sudo passwd username
Delete a user:
sudo deluser username # Debian/Ubuntu sudo userdel username # RHEL/CentOS/Fedora
To also remove the user’s home directory:
sudo deluser --remove-home username sudo userdel -r username
Modify a user: Use
usermodto change user properties:sudo usermod -g groupname username # Change primary group sudo usermod -aG groupname username # Add to supplementary group sudo usermod -s /bin/zsh username # Change shell sudo usermod -L username # Lock account sudo usermod -U username # Unlock account
3. Managing Groups
Groups help organize users and assign permissions efficiently.
Common Group Commands
Create a group:
sudo groupadd groupname
Delete a group:
sudo groupdel groupname
Add a user to a group:
sudo usermod -aG groupname username
The
-aGflag ensures the user is added to the new group without losing membership in existing ones.Remove a user from a group: There's no direct command, but you can edit group membership manually:
sudo gpasswd -d username groupname
View group membership:
groups username
Or view all groups a user belongs to via:
id username
List all groups on the system:
cut -d: -f1 /etc/group
4. Key Configuration Files
Linux stores user and group data in plain-text files under /etc:
/etc/passwd: Contains user account info (username, UID, GID, home directory, shell)./etc/shadow: Stores encrypted passwords and password aging (readable only by root)./etc/group: Defines groups and their members./etc/gshadow: Group password and admin info (rarely used).
?? Never edit these files directly unless necessary. Use the proper commands to avoid syntax errors or lockouts.
5. Best Practices for User and Group Management
- Avoid using root for daily tasks: Create a regular user with
sudoaccess instead. - Use groups for access control: For example, add users to the
dockergroup to run Docker commands withoutsudo. - Regularly audit accounts:
sudo less /etc/passwd sudo awk -F: '$3 == 0 {print $1}' /etc/passwd # Find all UID 0 accounts - Enforce strong passwords using PAM modules or tools like
passwd --stdinin scripts (with caution). - Disable unused accounts:
sudo usermod -L username
- Set appropriate default permissions via
/etc/login.defsand/etc/default/useradd.
6. Practical Example: Setting Up a Developer Team
Suppose you want to set up a team working on a shared project:
# Create a group for developers sudo groupadd developers # Create users and add them to the group sudo adduser alice sudo adduser bob sudo usermod -aG developers alice sudo usermod -aG developers bob # Create a shared directory sudo mkdir /srv/project sudo chown :developers /srv/project sudo chmod 775 /srv/project
Now both users can read, write, and execute in /srv/project, thanks to group permissions.
Managing users and groups in Linux isn’t complicated once you know the right tools. By using adduser, usermod, groupadd, and related commands wisely—and following security best practices—you can maintain a clean, secure, and well-organized system.
Basically, it's about knowing who needs access to what, and using groups to make that manageable.
The above is the detailed content of A Guide to Linux User and Group Management. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undress AI Tool
Undress images for free

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Install LXC (Linux Containers) in RHEL, Rocky & AlmaLinux
Jul 05, 2025 am 09:25 AM
Install LXC (Linux Containers) in RHEL, Rocky & AlmaLinux
Jul 05, 2025 am 09:25 AM
LXD is described as the next-generation container and virtual machine manager that offers an immersive for Linux systems running inside containers or as virtual machines. It provides images for an inordinate number of Linux distributions with support
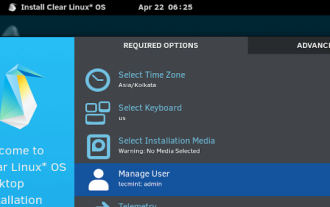 Clear Linux Distro - Optimized for Performance and Security
Jul 02, 2025 am 09:49 AM
Clear Linux Distro - Optimized for Performance and Security
Jul 02, 2025 am 09:49 AM
Clear Linux OS is the ideal operating system for people – ahem system admins – who want to have a minimal, secure, and reliable Linux distribution. It is optimized for the Intel architecture, which means that running Clear Linux OS on AMD sys
 How to create a self-signed SSL certificate using OpenSSL?
Jul 03, 2025 am 12:30 AM
How to create a self-signed SSL certificate using OpenSSL?
Jul 03, 2025 am 12:30 AM
The key steps for creating a self-signed SSL certificate are as follows: 1. Generate the private key, use the command opensslgenrsa-outselfsigned.key2048 to generate a 2048-bit RSA private key file, optional parameter -aes256 to achieve password protection; 2. Create a certificate request (CSR), run opensslreq-new-keyselfsigned.key-outselfsigned.csr and fill in the relevant information, especially the "CommonName" field; 3. Generate the certificate by self-signed, and use opensslx509-req-days365-inselfsigned.csr-signk
 How to extract a .tar.gz or .zip file?
Jul 02, 2025 am 12:52 AM
How to extract a .tar.gz or .zip file?
Jul 02, 2025 am 12:52 AM
Decompress the .zip file on Windows, you can right-click to select "Extract All", while the .tar.gz file needs to use tools such as 7-Zip or WinRAR; on macOS and Linux, the .zip file can be double-clicked or unzip commanded, and the .tar.gz file can be decompressed by tar command or double-clicked directly. The specific steps are: 1. Windows processing.zip file: right-click → "Extract All"; 2. Windows processing.tar.gz file: Install third-party tools → right-click to decompress; 3. macOS/Linux processing.zip file: double-click or run unzipfilename.zip; 4. macOS/Linux processing.tar
 7 Ways to Speed Up Firefox Browser in Linux Desktop
Jul 04, 2025 am 09:18 AM
7 Ways to Speed Up Firefox Browser in Linux Desktop
Jul 04, 2025 am 09:18 AM
Firefox browser is the default browser for most modern Linux distributions such as Ubuntu, Mint, and Fedora. Initially, its performance might be impressive, however, with the passage of time, you might notice that your browser is not as fast and resp
 How to troubleshoot DNS issues on a Linux machine?
Jul 07, 2025 am 12:35 AM
How to troubleshoot DNS issues on a Linux machine?
Jul 07, 2025 am 12:35 AM
When encountering DNS problems, first check the /etc/resolv.conf file to see if the correct nameserver is configured; secondly, you can manually add public DNS such as 8.8.8.8 for testing; then use nslookup and dig commands to verify whether DNS resolution is normal. If these tools are not installed, you can first install the dnsutils or bind-utils package; then check the systemd-resolved service status and configuration file /etc/systemd/resolved.conf, and set DNS and FallbackDNS as needed and restart the service; finally check the network interface status and firewall rules, confirm that port 53 is not
 Install Guacamole for Remote Linux/Windows Access in Ubuntu
Jul 08, 2025 am 09:58 AM
Install Guacamole for Remote Linux/Windows Access in Ubuntu
Jul 08, 2025 am 09:58 AM
As a system administrator, you may find yourself (today or in the future) working in an environment where Windows and Linux coexist. It is no secret that some big companies prefer (or have to) run some of their production services in Windows boxes an
 How would you debug a server that is slow or has high memory usage?
Jul 06, 2025 am 12:02 AM
How would you debug a server that is slow or has high memory usage?
Jul 06, 2025 am 12:02 AM
If you find that the server is running slowly or the memory usage is too high, you should check the cause before operating. First, you need to check the system resource usage, use top, htop, free-h, iostat, ss-antp and other commands to check CPU, memory, disk I/O and network connections; secondly, analyze specific process problems, and track the behavior of high-occupancy processes through tools such as ps, jstack, strace; then check logs and monitoring data, view OOM records, exception requests, slow queries and other clues; finally, targeted processing is carried out based on common reasons such as memory leaks, connection pool exhaustion, cache failure storms, and timing task conflicts, optimize code logic, set up a timeout retry mechanism, add current limit fuses, and regularly pressure measurement and evaluation resources.







