CakePHP is an open-source tool used to implement dynamic programming applications as well as it provides a different kind of functionality to the developer. Validation is one of the functionalities that is provided by the CakePHP, by using validation we can provide the validation to the arbitrary arrays of data as per our requirement. In CakePHP, we need to build the entities before the data validation in terms of shape and size. Here we also need to consider default entities, these entities will be validated before the conversation of entities. We can also apply validation rules as per our requirements.
Start Your Free Software Development Course
Web development, programming languages, Software testing & others
What is CakePHP Validation?
Information approval is a significant piece of any application, as it assists with ensuring that the information in a Model adjusts to the business rules of the application. For instance, you should ensure that passwords are somewhere around eight characters in length, or guarantee that usernames are special. Characterizing approval rules makes structure dealing with a whole lot simpler.
There are various perspectives to the approval cycle. What we’ll cover in this segment is the model side of things. Basically: what happens when you call the save () technique for your model. For more data about how to deal with the showing of approval blunders.
CakePHP Validation Methods
Now let’s see different validation methods in CakePHP as follows.
1. Add
Adds another standard to a field’s standard set. On the off chance that subsequent contention is a cluster, the rules list for the field will be supplanted with second contention and third contention will be overlooked.
Syntax
Add(string $specified field, array|string $specified name, array|Cake\Validation\ValidationRule $required rule [])
Explanation
In the above syntax, we use the add method with different parameters. In the above syntax specified name is used to define the name of the rule that we need to add. The array is used to define this rule or multiple rules as per requirement and this returns $this.
2. allowEmpty
By using this method, we can allow empty field
Syntax
allowEmpty(string $specified field, boolean|string|callable $whentrue, string|null msgull)
Explanation
In the above syntax, we use the add method with different parameters. In the above syntax specified name is used to define the name of the rule that we need to add. A boolean parameter is used to indicate when we empty we need to allow, here we can also validate in terms of true or false when we perform create or update operation. The message is used to show the message field and this returns $this.
3. Alphanumeric
By using this method, we can add alphanumeric rules to the field as per our requirements.
Syntax
alphanumeric (string $specified field, string|null $Msgnull, string|callable|null $whennull)
Explanation
In the above syntax, we use the alphanumeric method with different parameters. In the above syntax specified name is used to define the name of the rule that we need to add. Adds another standard to a field’s standard set. In the event that subsequent contention is a cluster, the rules list for the field will be supplanted with second contention and third contention will be overlooked and it returns $this.
4. Creditcard
By using this method, we can add credit card rules to the specified field as per requirement.
Syntax
creditCard(string $specified field , string $type'all', string|null $msgnull, string|callable|null $whennull)
Explanation
In the above syntax, we use the credit card method to add the rule with different parameters. The field you need to apply the standard to.
The sort of cards you need to permit. Defaults to ‘a(chǎn)ll’. You can likewise supply a variety of acknowledged card types, for instance, ‘mastercard’, ‘visa’, ‘a(chǎn)mex’.
The mistake message when the standard falls flat. Either ‘make’ or ‘update’ or a callable that profits valid, when the approval rule ought to be applied and it returns $this.
5. Email
By using this method, we can add an email validation rule to the field as per our requirement.
Syntax
Email(string $specified field , boolean $checkMXfalse, string|null $msgnull, string|callable|null, $whennull)
Explanation
By using the above syntax, we can implement the email validation rule. The field you need to apply the standard too.
Regardless of whether to check the MX records.
The blunder message when the standard fizzles.
Either ‘make’ or ‘update’ or a callable that profits valid, when the approval rule ought to be applied.
6. maxLength
By using this method, we can apply string validation to the field.
Syntax
maxLength(string $specified field, integer $max, string|null $msgnull, string|callable|null $whennull)
Explanation
In the above syntax, we use the maxLength method with different parameters. Here the specified field is used to define the field to which we want to apply the rule, max is used to define the maximum length of string, msgnull is used to show an error message when the rule fails.
7. minLength
By using this method, we can apply string validation to the field.
Syntax
minLength(string $specified field, integer $min, string|null $msgnull, string|callable|null $whennull)
Explanation
In the above syntax, we use the minLength method with different parameters. Here the specified field is used to define the field which we want to apply the rule, min is used to define the minimum length of string, msgnull is used to show an error message when the rule fails.
How to Create CakePHP Validation?
Now let’s see how we can create CakePHP validation with examples as follows.?First, we need to make the changes in routes.php file as follows.
<?php
use Cake\Http\Middleware\CsrfProtectionMiddleware;
use Cake\Routing\Route\DashedRoute;
use Cake\Routing\RouteBuilder;
$routes->setRouteClass(DashedRoute::class);
$routes->scope('/', function (RouteBuilder $builder) {
$builder->registerMiddleware('csrf', new CsrfProtectionMiddleware([
'httpOnly' => true,
]));
$builder->applyMiddleware('csrf');
//$builder->connect('/pages',['controller'=>'Pages','action'=>'display', 'home']);
$builder->connect('validation',['controller'=>'Valid','action'=>'index']);
$builder->fallbacks();
});
?>
Now create an index.php file and write the following code as follows.
<?php
if($errors) {
foreach($errors as $error)
foreach($error as $mssg)
echo '<font color="red">'.$mssg.'</font><br>';
} else {
echo "There is no errors.";
}
echo $this->Form->create(NULL,array('url'=>'/validation'));
echo $this->Form->control('username of person');
echo $this->Form->control('password');
echo $this->Form->button('Submit');
echo $this->Form->end();
?>
Now execute the above code we will get the following screen as shown below screenshot.
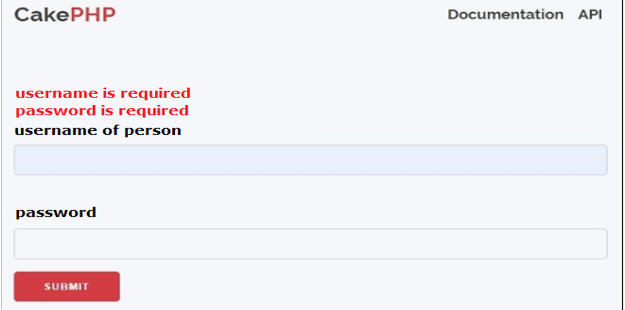
Suppose let’s consider, if we enter only password then it shows username is required as shown in the following screenshot.
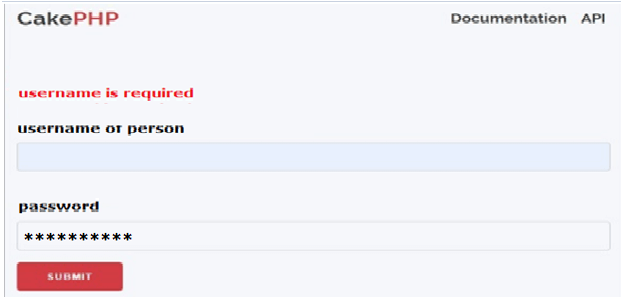
Similarly, we can apply validation for username of person filed as shown in the following screenshot as follows.

In this way, we can implement different methods such as to get, post as per our requirement.
Conclusion
We hope from this article you learn more about the CakePHP validation. From the above article, we have taken in the essential idea of the CakePHP validation and we also see the representation and example of the CakePHP validation. From this article, we learned how and when we use the CakePHP validation.
The above is the detailed content of CakePHP Validation. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undress AI Tool
Undress images for free

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to use JavaScript to determine whether two arrays are equal?
May 23, 2025 pm 10:51 PM
How to use JavaScript to determine whether two arrays are equal?
May 23, 2025 pm 10:51 PM
In JavaScript, you need to use a custom function to determine whether two arrays are equal, because there is no built-in method. 1) Basic implementation is to compare lengths and elements, but cannot process objects and arrays. 2) Recursive depth comparison can handle nested structures, but requires special treatment of NaN. 3) Special types such as functions and dates need to be considered, and further optimization and testing are required.
 How to verify social security number string in PHP?
May 23, 2025 pm 08:21 PM
How to verify social security number string in PHP?
May 23, 2025 pm 08:21 PM
Social security number verification is implemented in PHP through regular expressions and simple logic. 1) Use regular expressions to clean the input and remove non-numeric characters. 2) Check whether the string length is 18 bits. 3) Calculate and verify the check bit to ensure that it matches the last bit of the input.
 How to correctly handle this pointing in a closure?
May 21, 2025 pm 09:15 PM
How to correctly handle this pointing in a closure?
May 21, 2025 pm 09:15 PM
The methods to correctly handle this pointing in JavaScript closures include: 1. Use arrow functions, 2. Use bind methods, 3. Use variables to save this. These methods ensure that this intrinsic function correctly points to the context of the external function.
 How to implement data encryption with JavaScript?
May 23, 2025 pm 11:12 PM
How to implement data encryption with JavaScript?
May 23, 2025 pm 11:12 PM
Using JavaScript to implement data encryption can use the Crypto-JS library. 1. Install and introduce the Crypto-JS library. 2. Use the AES algorithm for encryption and decryption to ensure that the same key is used. 3. Pay attention to the secure storage and transmission of keys. It is recommended to use CBC mode and environment variables to store keys. 4. Consider using WebWorkers when you need high performance. 5. When processing non-ASCII characters, you need to specify the encoding method.
 How to define constructors in PHP?
May 23, 2025 pm 08:27 PM
How to define constructors in PHP?
May 23, 2025 pm 08:27 PM
In PHP, the constructor is defined by the \_\_construct magic method. 1) Define the \_\_construct method in the class, which will be automatically called when the object is instantiated and is used to initialize the object properties. 2) The constructor can accept any number of parameters and flexibly initialize the object. 3) When defining a constructor in a subclass, you need to call parent::\_\_construct() to ensure that the parent class constructor executes. 4) Through optional parameters and conditions judgment, the constructor can simulate the overload effect. 5) The constructor should be concise and only necessary initialization should be done to avoid complex logic or I/O operations.
 Detailed steps to deploy a Joomla website on PhpStudy
May 16, 2025 pm 08:00 PM
Detailed steps to deploy a Joomla website on PhpStudy
May 16, 2025 pm 08:00 PM
The steps to deploy a Joomla website on PhpStudy include: 1) Configure PhpStudy, ensure that Apache and MySQL services run and check PHP version compatibility; 2) Download and decompress PhpStudy's website from the official Joomla website, and then complete the installation through the browser according to the installation wizard; 3) Make basic configurations, such as setting the website name and adding content.
 PHP Dependency Injection: Benefits and Examples
May 17, 2025 am 12:14 AM
PHP Dependency Injection: Benefits and Examples
May 17, 2025 am 12:14 AM
The benefits of using dependency injection (DI) in PHP include: 1. Decoupling, making the code more modular; 2. Improve testability and easy to use Mocks or Stubs; 3. Increase flexibility and facilitate reusing of dependencies; 4. Improve reusability, and the classes can be used in different environments. By passing dependencies externally to objects, DI makes the code easier to maintain and extend.
 PHP Email Tutorial: Sending Emails Made Easy
May 19, 2025 am 12:10 AM
PHP Email Tutorial: Sending Emails Made Easy
May 19, 2025 am 12:10 AM
SendingemailswithPHPisstraightforwardusingthemail()functionormoreadvancedlibrarieslikePHPMailer.1)Usemail()forbasicemails,settingrecipients,subjects,messages,andheaders.2)ForHTMLemails,adjustheaderstospecifyHTMLcontent.3)EmployPHPMailerforenhancedfea






